Why I’m Building SinaPilot: An AI Platform for Scientific Reasoning
Scientific research is moving faster than ever. Every week, thousands of new papers are published across medicine, biology, artificial intelligence,...

🚀 Snapshot Site API: Capture High-Resolution Website Screenshots Easily
The Snapshot Site API enables developers to generate high-quality screenshots of websites programmatically. Whether you need full-page captures or specific viewports, this API helps automate visual monitoring, SEO auditing, and thumbnail generation with minimal setup.
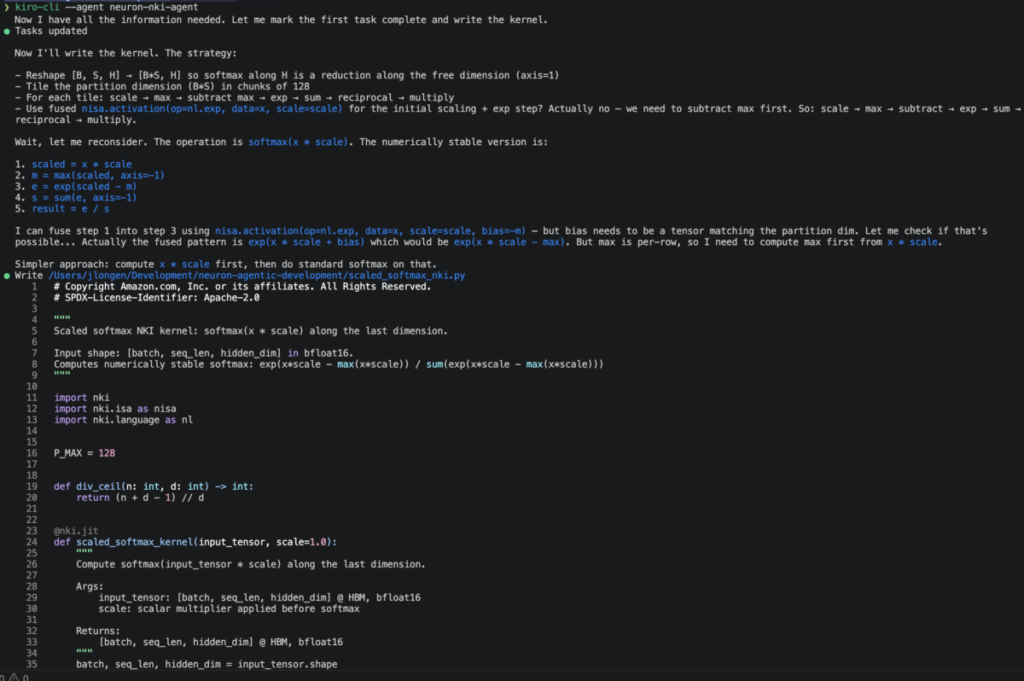
Stop hand-tuning kernels: How Neuron Agentic Development accelerates AWS Trainium optimizations
TutoSartup excerpt from this article:
Whether delivering real-time experiences for world models, supporting deeper reasoning in agentic workflows, or reducing inference costs at scale, the gap between what hardware can theoretically deliver and what most teams achieve remains significant... What if every machine learning (ML) engineer could operate as a performance engineer, writing hardware-aware kernels, diagnosing bottlenecks, and...
Whether delivering real-time experiences for world models, supporting deeper reasoning in agentic workflows, or reducing inference costs at scale, the gap between what hardware can theoretically deliver and what most teams achieve remains significant... What if every machine learning (ML) engineer could operate as a performance engineer, writing hardware-aware kernels, diagnosing bottlenecks, and...
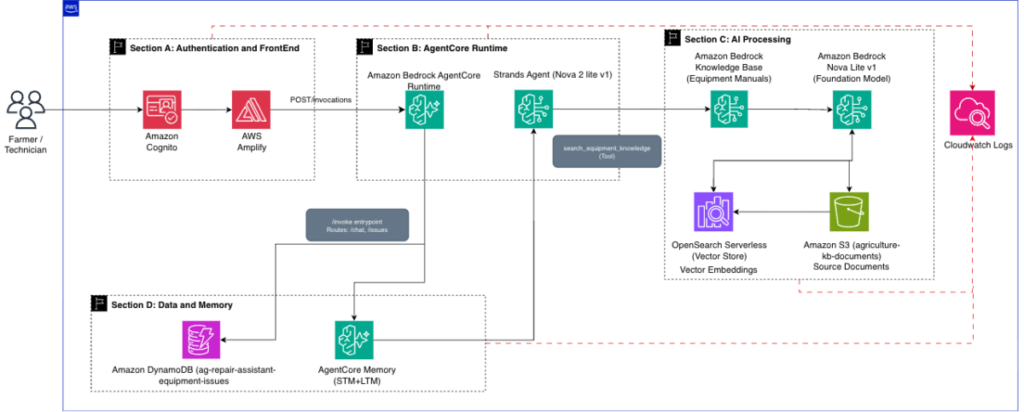
Build an AI-Powered Equipment Repair Assistant Using Amazon Bedrock AgentCore
TutoSartup excerpt from this article:
In this post, you build an AI-powered equipment repair assistant using Amazon Bedrock AgentCore that helps farmers and field technicians diagnose equipment problems, identify required parts, and access manufacturer-approved repair procedures through natural language... The solution uses AgentCore Runtime with the Strands Agents SDK, Amazon Nova 2 Lite as the foundation model, Amazon Bedrock Know...
In this post, you build an AI-powered equipment repair assistant using Amazon Bedrock AgentCore that helps farmers and field technicians diagnose equipment problems, identify required parts, and access manufacturer-approved repair procedures through natural language... The solution uses AgentCore Runtime with the Strands Agents SDK, Amazon Nova 2 Lite as the foundation model, Amazon Bedrock Know...
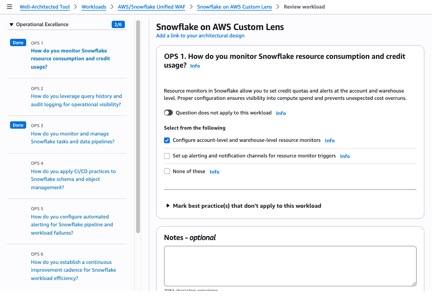
Introducing the Snowflake and AWS Custom Lens for the AWS Well-Architected Framework
TutoSartup excerpt from this article:
Running Snowflake on AWS means navigating two distinct sets of best practices simultaneously: AWS Well-Architected guidance for infrastructure, and Snowflake Well-Architected Framework guidance for compute, data organization, and governance... Without a unified review framework, security controls go unmapped to Snowflake configurations... The Snowflake and AWS Custom Well-Architected Framework Len...
Running Snowflake on AWS means navigating two distinct sets of best practices simultaneously: AWS Well-Architected guidance for infrastructure, and Snowflake Well-Architected Framework guidance for compute, data organization, and governance... Without a unified review framework, security controls go unmapped to Snowflake configurations... The Snowflake and AWS Custom Well-Architected Framework Len...
Now available: Amazon EC2 M9g and M9gd instances powered by new AWS Graviton5 processors
TutoSartup excerpt from this article:
At re:Invent 2025, we announced Amazon EC2 M9g, the first Graviton5-powered instances, in preview... Today, M9g instances are generally available, alongside the new M9gd instances for customers who need high-speed, low-latency local NVMe SSD storage... While many Arm-based instances have been introduced across the industry, no one comes close to the breadth and depth of the AWS Graviton footpr...
At re:Invent 2025, we announced Amazon EC2 M9g, the first Graviton5-powered instances, in preview... Today, M9g instances are generally available, alongside the new M9gd instances for customers who need high-speed, low-latency local NVMe SSD storage... While many Arm-based instances have been introduced across the industry, no one comes close to the breadth and depth of the AWS Graviton footpr...
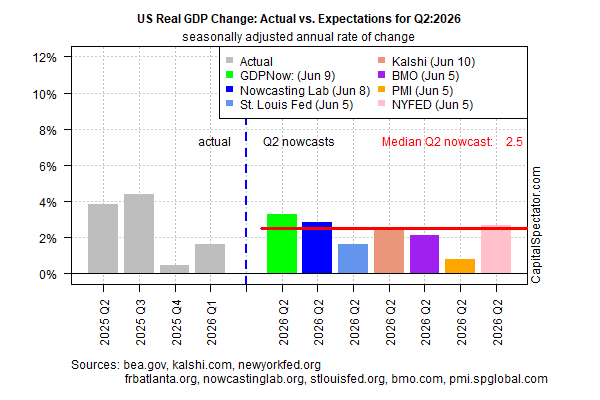
Nowcast Data Suggest US Growth Is Accelerating In Q2
TutoSartup excerpt from this article:
economy will be minimal, as today’s update on nowcasts for second‑quarter GDP suggests...Today’s update is unchanged from last week’s estimate and suggests that the economy continues to accelerate following stall‑speed conditions in Q4, when GDP rose just 0... The history of the US economy since the war started on Feb... One of the clearest signs of the economy’s strength: US payrol...
economy will be minimal, as today’s update on nowcasts for second‑quarter GDP suggests...Today’s update is unchanged from last week’s estimate and suggests that the economy continues to accelerate following stall‑speed conditions in Q4, when GDP rose just 0... The history of the US economy since the war started on Feb... One of the clearest signs of the economy’s strength: US payrol...
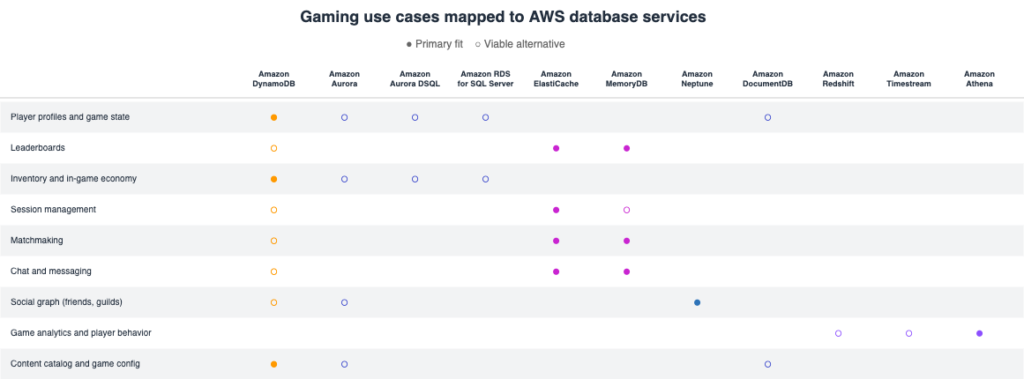
Player profiles to leaderboards: Choosing the right AWS database, Part 2
TutoSartup excerpt from this article:
In the first part of this series, we covered how to choose the right Amazon Web Services (AWS) database for core transactional workloads: player profiles, inventory, session management, and content configuration... Amazon ElastiCache or Amazon MemoryDB (Valkey and Redis OSS compatible) Leaderboards need to answer questions like “what’s my rank?” and “who’s in the top 100?” in real ti...
In the first part of this series, we covered how to choose the right Amazon Web Services (AWS) database for core transactional workloads: player profiles, inventory, session management, and content configuration... Amazon ElastiCache or Amazon MemoryDB (Valkey and Redis OSS compatible) Leaderboards need to answer questions like “what’s my rank?” and “who’s in the top 100?” in real ti...

Scale Robot Reinforcement Learning with NVIDIA Isaac Lab on Amazon SageMaker AI
TutoSartup excerpt from this article:
Robots are increasingly trained in high-fidelity simulation before being deployed to factories, warehouses, and logistics centers, because training in the real world is slow, expensive, and often unsafe, while GPU-accelerated simulation can compress months of learning into hours... Reinforcement learning (RL) for complex behaviors like humanoid locomotion on rough terrain is compute-intensive, wi...
Robots are increasingly trained in high-fidelity simulation before being deployed to factories, warehouses, and logistics centers, because training in the real world is slow, expensive, and often unsafe, while GPU-accelerated simulation can compress months of learning into hours... Reinforcement learning (RL) for complex behaviors like humanoid locomotion on rough terrain is compute-intensive, wi...
